Digital Forensics for Employment Investigations
An employee resigns on Friday and gives back their laptop.
On Monday, you find out they’ve started a competing company and they’re calling your clients.
Everything they took — files, contacts, client data, proposal templates — is on the laptop they just returned. And they wiped it before handing it in.
This is the most common scenario we see in employment-related digital investigations. And in most cases, the data isn’t actually gone.
What Types of Employment Cases Use Digital Forensics
Trade secret theft: Former employees copying proprietary data to USB drives, personal email, or cloud storage before departure. Forensic examination recovers the transfer logs.
IP misappropriation: An employee develops code, designs, or client materials at work, then claims ownership after leaving. Device forensics establishes where the work was actually created and under what circumstances.
Hostile work environment: Claims of harassing text messages, emails, or communications require authenticated evidence. Forensic examination of the device provides that authentication.
Expense fraud: Digital forensics of business accounts and mobile devices surfaces fabricated receipts, vendor arrangements, and financial irregularities.
Insider threat / data exfiltration: Employee sharing sensitive data with a competitor, foreign entity, or personal accounts. Network logs combined with device forensics traces the flow of data.
Non-compete violations: An employee subject to a non-compete contacts your clients from their personal phone. Those communications are potentially recoverable and documentable.
What Can Be Recovered From a Company-Issued Device
On a company-issued laptop:
On a company-issued smartphone:
What You Can and Can’t Examine as an Employer
Company-issued devices: Employers have wide latitude to examine devices they own. A clear device policy (ideally signed at onboarding) establishes the expectation of no privacy on company equipment and the employer’s right to monitor and examine.
Personal devices with company data: This is legally complex. If an employee accessed company systems on their personal phone (via MDM, corporate email app, or VPN), the employer may have the right to examine the corporate app data — but not the entire personal device. This requires careful legal guidance before examination.
Personal accounts on company devices: If an employee logged into their personal Gmail or personal iCloud on a company laptop, the company generally can’t access those personal accounts — even on a company device. The boundary is between company data and personal data, not company device vs. personal device.
Always get legal counsel’s sign-off on the examination scope before beginning.
Legal Considerations Before You Start
Computer Fraud and Abuse Act (CFAA): Unauthorized access to computer systems, even by employers, can create liability. Ensure your authority to examine the device is clear and documented before proceeding.
California Penal Code § 502: California’s anti-hacking statute is broad. Employer device examination is generally protected when the device is company-owned and a clear policy exists, but the details matter.
Evidence preservation: If litigation is anticipated, treat this as a litigation matter from day one. Document chain of custody, hash the device, and use a certified examiner. Evidence gathered sloppily now becomes unusable later.
HR investigation privilege: Coordinate with legal counsel on whether the forensic investigation falls under attorney-client privilege. Involving counsel from the start can protect the investigation from disclosure.
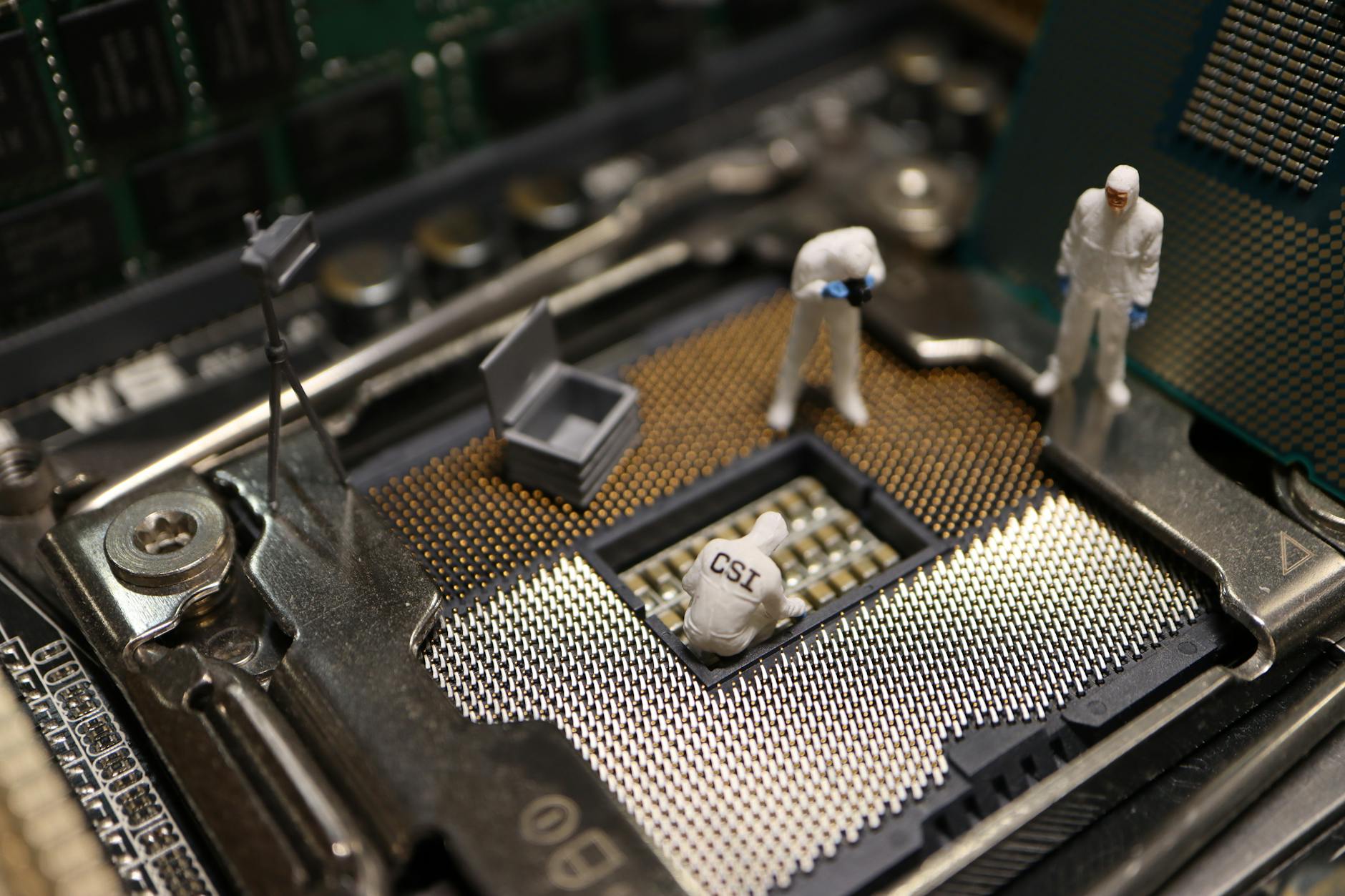
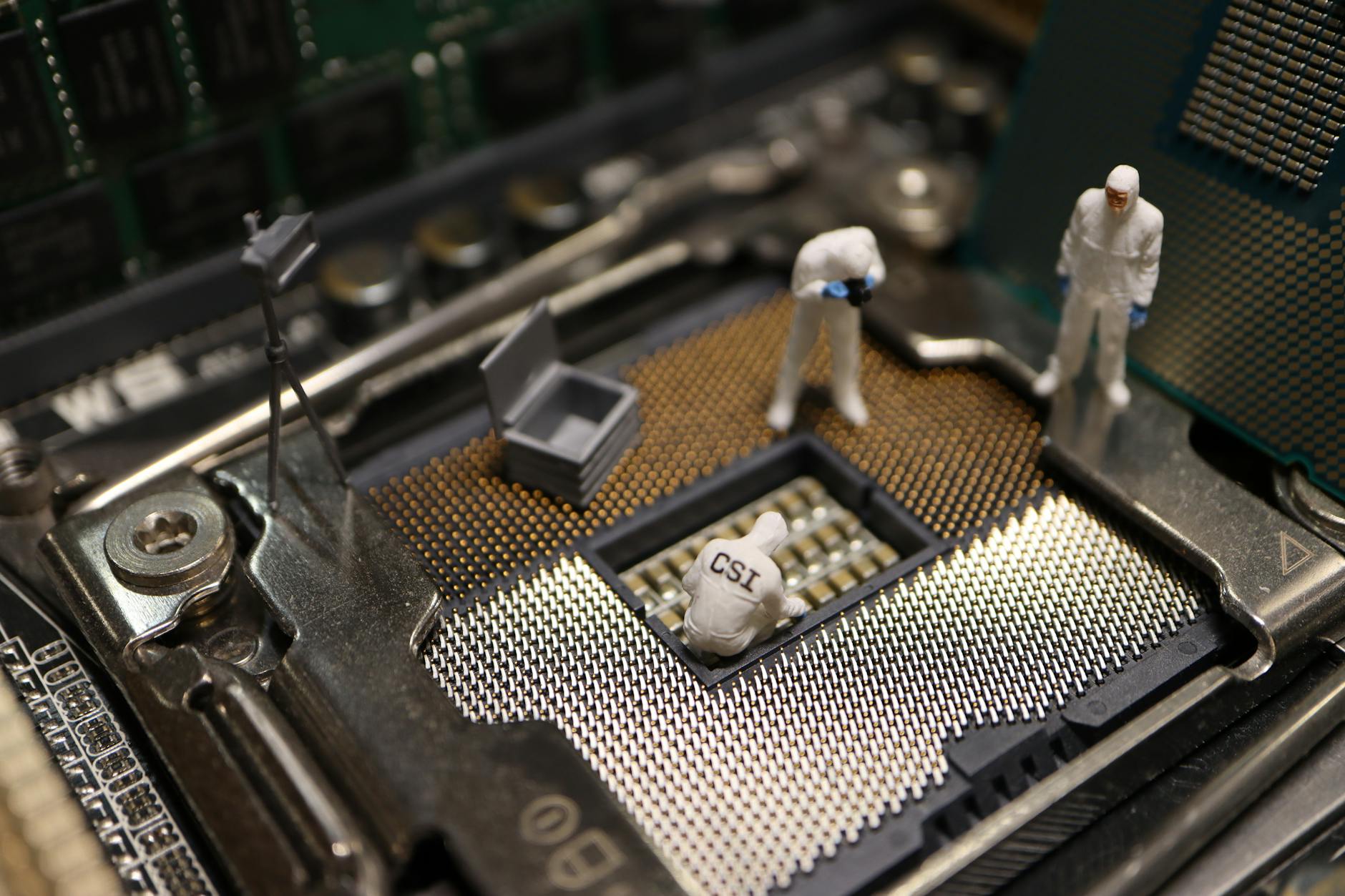
The Forensic Process for Employment Cases
1. Secure the device immediately — the moment the investigation is triggered, the device should be taken out of the employee’s access and stored securely. Every minute it remains in their possession is a minute they could be deleting data.
2. Do not let IT perform the forensic examination — IT staff are not forensic examiners. Well-meaning IT departments routinely destroy evidence by using standard recovery tools or accessing the device without proper methodology. Use a certified forensic examiner.
3. Document chain of custody from seizure — who took the device, when, where it was stored, who else had access.
4. Run the extraction before any IT actions — before the laptop is re-imaged for the next employee, before the phone is factory reset, run the forensic examination.
5. Produce a report formatted for legal use — if this ends up in arbitration or litigation, you need a report that satisfies evidentiary standards, not just an IT summary.
How Long Does Evidence Last on a Device?
Faster than most employers realize, evidence disappears:
The moment you suspect a problem, act. Do not wait for HR to complete their administrative investigation before engaging a forensic examiner.
FAQ
Can I examine a former employee’s personal phone if they used it for work?
Only the corporate app data, and only if your MDM or BYOD policy grants that access. Examining personal data on a personal device without consent or a court order exposes the company to liability.
What if the employee claims the data was backed up to their personal cloud?
That’s a more complex problem — you’d need a court order to compel access to personal cloud accounts. Document the corporate data that existed on the company device before they left and focus on the damage calculation from that evidence.
How is forensic evidence used in arbitration vs. court?
Arbitration proceedings generally follow the same evidence rules as courts for matters of authentication and chain of custody. A forensic report that would be admissible in court is admissible in arbitration. The procedural timelines are often faster, which makes rapid evidence preservation even more critical.
Employment Investigation Forensics in San Diego
Octo Digital Forensics handles corporate device examinations, IP theft investigations, and employment dispute forensics for businesses and legal teams in San Diego.
Certified examiners. Court-ready reports. Confidential handling.
Visit octodf.com or call 858-692-3306.
See also: Ftc Investigation Forensics | Whistleblower Investigation | Nft Fraud Forensics
Need Professional Digital Forensics?
Octo Digital Forensics provides expert mobile forensics, data recovery, and digital investigation services for attorneys, insurance companies, and private investigators. Court-admissible reports. Certified examiners.
Contact: octodf.com | info@derickdowns.com | (858) 692-3306



