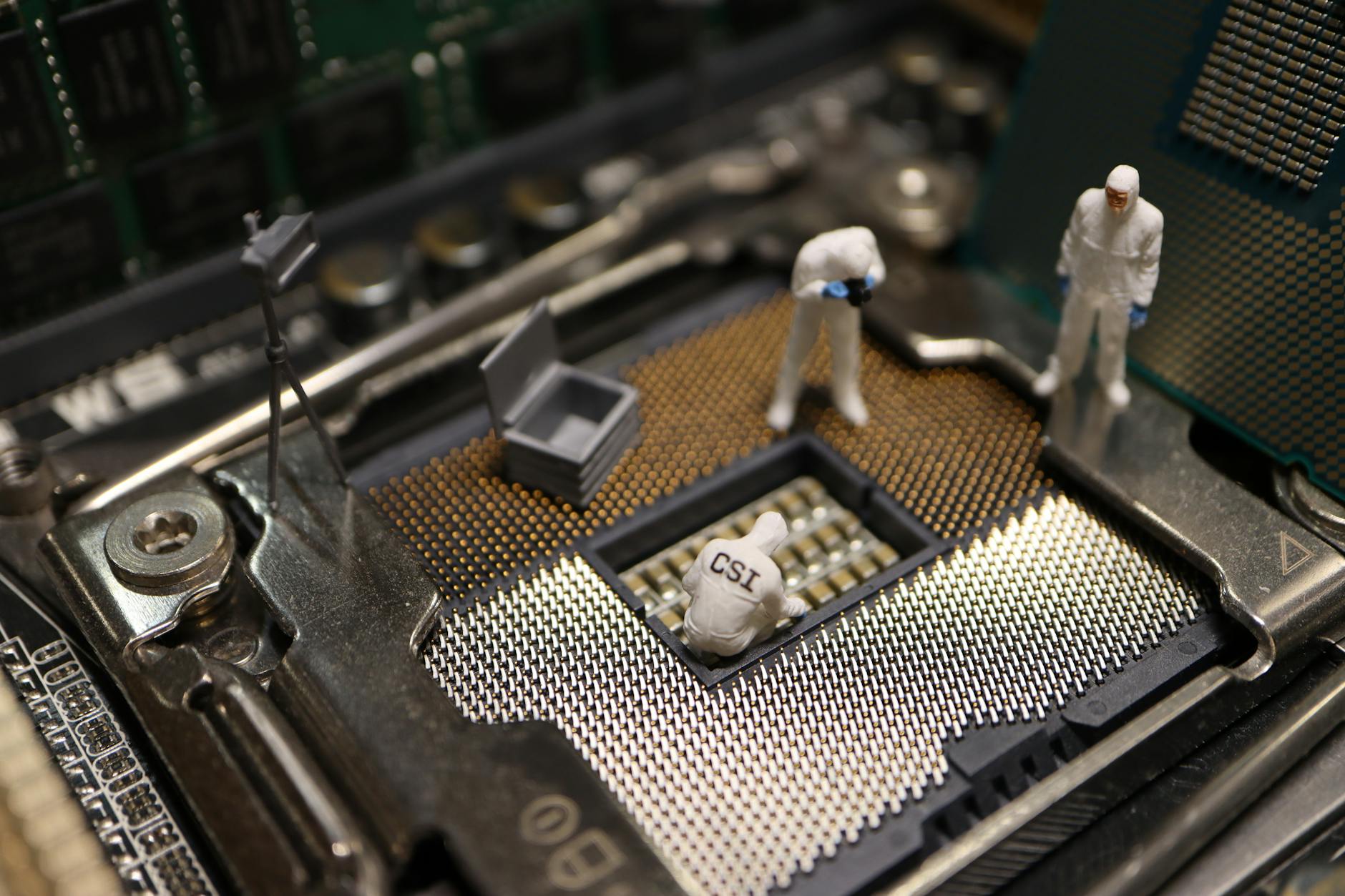
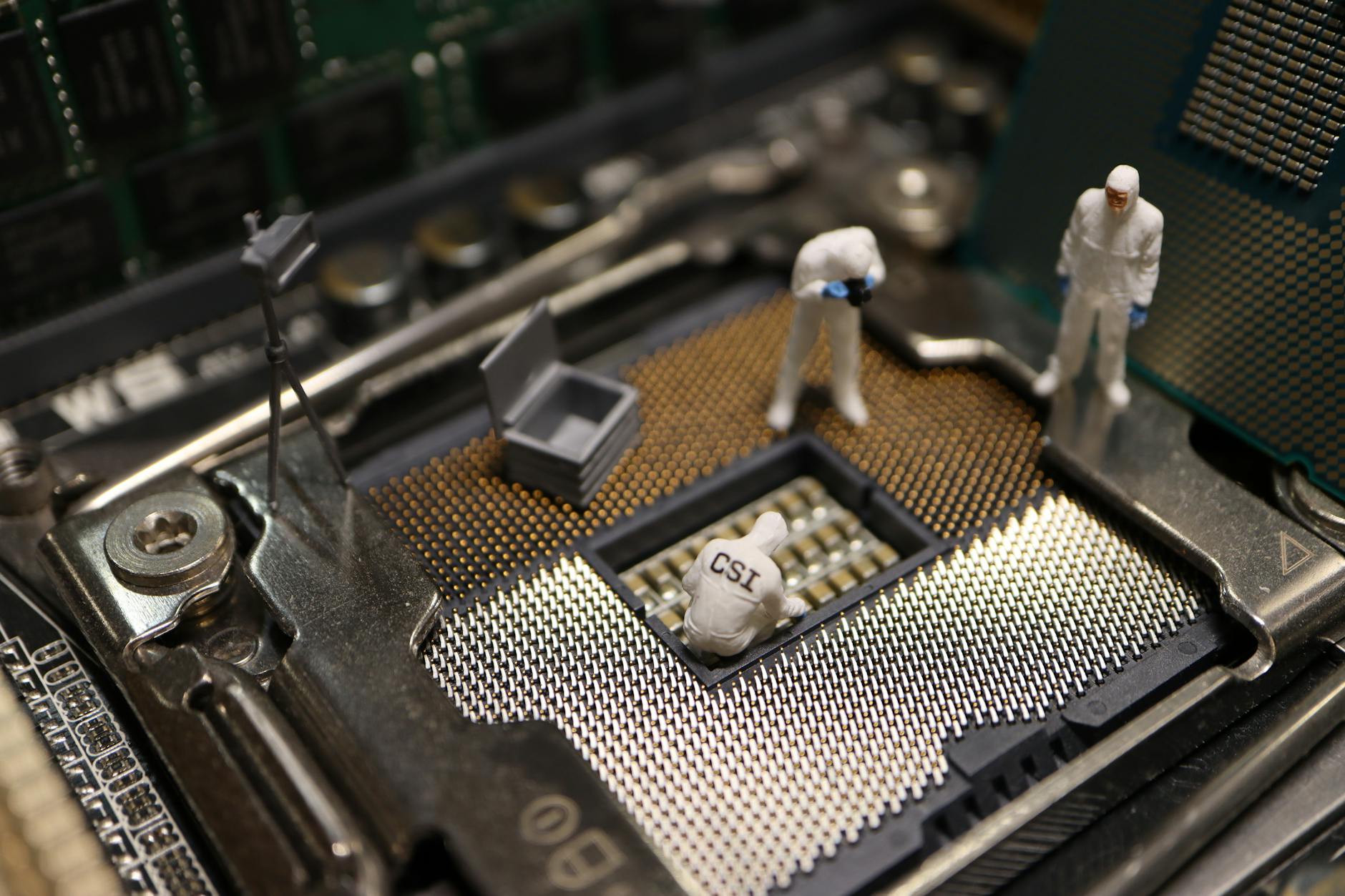
Phone Forensics for Criminal Defense: What Defense Attorneys Need to Know
Most defense attorneys think of phone forensics as something the prosecution does.
It’s not. It’s something every defense attorney should be using — on the state’s forensic evidence, on their client’s device, and on any other phone that might contain exculpatory data.
Here’s how to use digital forensics as a defense tool.

Challenging the State’s Forensic Evidence
The prosecution’s forensic report is not the end of the analysis. It’s the beginning of your investigation.
Start with these questions:
Was the device properly handled at seizure? If the phone wasn’t immediately placed in a Faraday bag (blocking all wireless signals) after seizure, it may have received data, synced to iCloud, or had its state altered before extraction. This is a foundational chain of custody issue.
Was the device locked or unlocked when seized? This matters enormously. An unlocked phone can be put into airplane mode to preserve its state. A locked phone that was seized and immediately placed in flight mode is in better shape than one that sat in a storage locker for two weeks receiving background app updates.
What extraction method was used? A logical extraction misses deleted data and many app databases. If the state did a logical extraction and is presenting it as complete, challenge the completeness.
What tool version was used? Get the specific version number. Research whether that version had any known issues with the device model. These details are rarely wrong, but when they are, the consequences are significant.
What wasn’t recovered? Ask for the examiner’s full notes, not just the summary report. What data categories produced no results? What did the tool flag as unavailable? The absence of data that should be there is as significant as the presence of data that is.
Using Your Client’s Phone in Their Defense
Your client’s phone is a timeline.
Before accepting the prosecution’s narrative of events, pull the phone data and build the actual timeline from it:
This is exculpatory evidence your client is carrying in their pocket. Get a certified examiner to pull it in a documented, chain-of-custody-backed way so it’s ready to use at trial.
Alibi Evidence Through Digital Forensics
Location evidence from a phone is among the most credible alibi evidence available.
A phone pinging a cell tower 30 miles from the crime scene at the time of the offense doesn’t prove your client was there — phones can be left places — but combined with other evidence, it creates reasonable doubt.
More precise: GPS coordinates embedded in a photo taken with the phone at a specific time, at a specific location that isn’t the crime scene, is extremely difficult to explain away.
What to request from the phone:
Pull data from the surrounding days too — not just the day of the alleged offense. Context matters.
Third-Party Device Investigations
The most overlooked tool in criminal defense: examining devices other than your client’s.
Victim devices: In cases where the alleged victim’s credibility is central, their phone may contain communications that contradict their account. Defense counsel can subpoena this data through proper channels.
Witness devices: A witness who changes their story may have prior communications inconsistent with their current testimony. Subpoena their records.
Third-party suspect devices: If another person had motive, opportunity, and access, their phone data might contain evidence pointing toward them and away from your client.
Building this evidentiary strategy requires a forensic examiner who understands defense practice and can be retained as a testifying expert.
The Brady Problem: Did the Prosecution Withhold Digital Evidence?
Prosecutors have a constitutional obligation to disclose exculpatory evidence (Brady v. Maryland). In the digital age, that includes exculpatory data from forensic examinations.
If the prosecution’s examiner ran a full extraction and only produced a subset of the data, ask:
Request the full extraction file, not just the PDF report. A forensic examiner retained by the defense can run the same file through their own analysis tools and find what the prosecution’s examiner either missed or omitted.
Expert Witness Testimony for the Defense
A defense-retained forensic expert can:
Juries understand credibility. When a qualified expert takes the stand and explains why the prosecution’s forensic evidence doesn’t prove what they claim it proves, it plants reasonable doubt.
FAQ
Can defense counsel examine the prosecution’s forensic expert before trial?
Yes. Through depositions in most jurisdictions, or preliminary hearing testimony in California criminal proceedings. Use the deposition questions outlined in the expert witness deposition guide and be thorough on methodology.
What if the prosecution refuses to produce the full forensic extraction file?
File a Brady motion with specific grounds. The complete extraction file is discovery material when the phone was examined by the state. Selective production of favorable excerpts from a forensic examination is a Brady violation waiting to be challenged.
How quickly can a defense forensic expert review the prosecution’s report?
A standard review of a forensic report and opinion letter runs 1-3 business days. A full rebuttal examination of the device (if it can be obtained) takes 3-7 business days. Start this process the moment you receive the prosecution’s report.
Forensic Support for Criminal Defense in San Diego
Octo Digital Forensics provides defense-side forensic examination, prosecution report review, and expert witness services for criminal defense attorneys throughout California.
Cellebrite-certified. Experience on both civil and criminal matters.
Visit octodf.com or call 858-692-3306.
See also: Criminal Defense Expert Witness | Testifying Plaintiff Vs Defense | Nft Fraud Forensics
Need Professional Digital Forensics?
Octo Digital Forensics provides expert mobile forensics, data recovery, and digital investigation services for attorneys, insurance companies, and private investigators. Court-admissible reports. Certified examiners.
Contact: octodf.com | info@derickdowns.com | (858) 692-3306