When an employee leaks confidential data, a business partner commits fraud, or internal systems are compromised, companies turn to digital forensics to find out what happened, who did it, and what was taken.
Getting a corporate investigation right — both technically and legally — requires careful coordination between forensics, legal counsel, and HR.
Common Corporate Investigation Scenarios
Data theft by departing employees: An employee takes client lists, proprietary documents, or trade secrets before resigning. USB drive activity, email forwarding, and cloud upload logs can document exactly what was taken.
Intellectual property theft: Competitors sometimes recruit employees to bring proprietary data. The forensic trail of copied files, emailed attachments, and external drive connections can prove misappropriation.
Expense fraud: Manipulated expense reports, altered receipts, or inflated vendor invoices leave digital traces in email, document metadata, and financial system records.
Business email compromise (BEC): Attackers compromise company email accounts to redirect wire transfers. Email forensics traces the access, the manipulation, and often the attackers’ IP addresses.
Insider trading: Employees who trade on material non-public information accessed through work systems. Email and document access logs can show what information was accessed and when.
Harassment and workplace misconduct: Text messages, email, internal chat systems (Slack, Teams), and social media posts are commonly relevant in workplace misconduct investigations.

The Legal Framework: Employee Privacy vs. Investigation Rights
Companies have broad rights to investigate activity on company-owned devices and networks. Key principles:
Acceptable use policies matter: A clear, acknowledged policy stating that employees have no expectation of privacy on company devices and networks is the foundation of a defensible investigation. Without it, investigations face legal challenges.
Personal devices: Company authority generally doesn’t extend to employees’ personal phones or personal email accounts. Exceptions exist for BYOD (Bring Your Own Device) programs with appropriate enrollment agreements.
Labor law considerations: In some jurisdictions, restrictions apply to monitoring employee communications even on company systems. Consult employment counsel before beginning any monitoring or investigation.
Notification requirements: Some states require employee notification of monitoring. Others don’t. This varies significantly by jurisdiction.
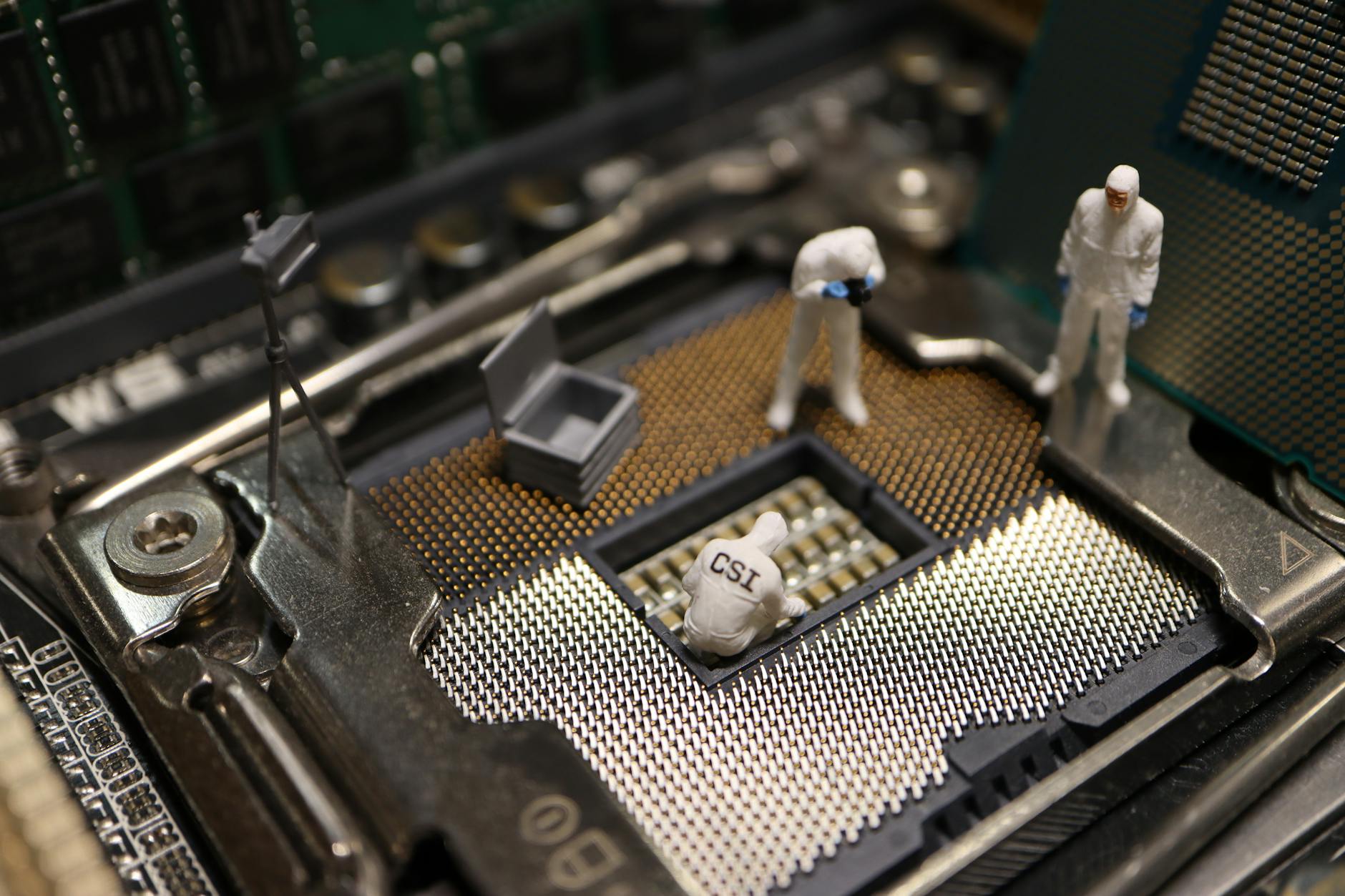
The Digital Forensics Process in Corporate Investigations
Step 1: Preservation
Before anyone’s devices are touched, preserve the evidence. Issue a litigation hold notice that instructs custodians to preserve relevant documents. Image devices before the subject knows an investigation is underway.
Step 2: Identification
Work with counsel to identify the relevant custodians, devices, and time periods. Corporate investigations involve data from email servers, endpoint devices, network logs, DLP systems, cloud collaboration tools, and HR systems.
Step 3: Collection
Forensic imaging of relevant devices. Collection of email from Exchange/M365. Collection of network logs. This should be done by or under the supervision of qualified forensic examiners.
Step 4: Analysis
Review the collected data for relevant evidence. Key artifacts:
Step 5: Reporting
A written report documenting findings — in language suitable for use by HR, legal counsel, and if necessary, law enforcement or courts.
eDiscovery and Corporate Litigation
Corporate litigation routinely involves massive volumes of digital data. eDiscovery is the process of identifying, collecting, processing, reviewing, and producing this data in response to legal hold requirements and court orders.
Key eDiscovery considerations:
Failing to preserve and produce relevant eDiscovery can result in sanctions, adverse inference instructions, or case-dispositive rulings.
FAQ: Corporate Digital Investigations
Q: Should we call law enforcement before conducting an internal investigation?
A: Not always immediately. Internal investigation first allows the company to assess scope and manage communications. Law enforcement referral often comes after the internal investigation establishes the facts. However, for active cybercrime or imminent harm, contact law enforcement promptly.
Q: Can we use evidence from a corporate investigation in a civil lawsuit against an employee?
A: Yes, if collected properly — on company devices with appropriate policies in place. Your counsel should review collection methodology before relying on it in litigation.
Q: How long does a corporate digital investigation take?
A: Simple single-device cases: 2–5 business days for analysis. Multi-device, multi-custodian investigations with email review can take weeks to months depending on data volume.
Q: How long does a typical forensic examination take?
A: Timelines vary based on data volume and case complexity. A single device may take one to three days; multi-device investigations can span weeks.
Q: What certifications should a digital forensics examiner hold?
A: Common certifications include EnCE, CFCE, CCE, and GCFE. Relevance depends on the examination type and the jurisdiction’s expectations.
Case Example
A financial services firm suspected an employee of sharing confidential client data. The forensic examiner imaged the workstation and email archive, revealing unusual file access during the employee’s final two weeks. Email metadata showed communications with a personal account containing attachments matching accessed files. USB device history confirmed a personal storage device was connected during access windows. The evidence was compiled into a report supporting both internal proceedings and civil litigation, leading to a preliminary injunction.
Practitioner Takeaways
- Verify forensic images with cryptographic hashing before analysis.
- Document every examination step for reproducibility.
- Cross-reference findings across multiple artifact types.
- Note tool versions used — behavior changes between versions affect reproducibility.
- Distinguish facts from inferences in your report.
See also: Whistleblower Investigation | Employment Investigation Forensics | Ftc Investigation Forensics
Need Professional Digital Forensics?
Octo Digital Forensics provides expert mobile forensics, data recovery, and digital investigation services for attorneys, insurance companies, and private investigators. Court-admissible reports. Certified examiners.
Contact: octodf.com | info@derickdowns.com | (858) 692-3306