Email is still one of the most common evidence sources in civil and criminal investigations — business disputes, fraud cases, harassment, employment matters, and financial crimes all generate email evidence.
Email forensics involves more than reading the messages. It’s about tracing where messages actually came from, recovering messages that were deleted, and authenticating that a message hasn’t been altered.
Email Header Analysis
Every email carries a header — a block of metadata that most email clients hide from users. The header tells the forensic story of where the message actually came from and how it traveled.
Key header fields:
Received headers: Each mail server that handled the email adds a “Received:” line. Reading them from bottom to top shows the complete path the email traveled — originating server, intermediate relays, and final delivery. Timestamps on each hop can confirm or contradict claimed send times.
X-Originating-IP: Many email services include the sender’s IP address in this field. This is the IP address of the device that sent the email — often the most important piece of data in a fraud or harassment investigation.
Message-ID: A globally unique identifier assigned by the originating server. Useful for correlating messages across different evidence sources.
DKIM signature: DomainKeys Identified Mail — a cryptographic signature that proves the email was actually sent by the claimed domain and wasn’t altered in transit. A valid DKIM signature is strong authentication. A missing or invalid signature doesn’t prove fraud but warrants further investigation.
SPF (Sender Policy Framework): A DNS record that specifies which IP addresses are authorized to send email for a domain. An SPF failure (“Fail” or “Softfail”) indicates the sending server isn’t authorized — a red flag for spoofed email.
DMARC: Combines SPF and DKIM with a reporting policy. DMARC pass provides strong assurance the email is legitimate.
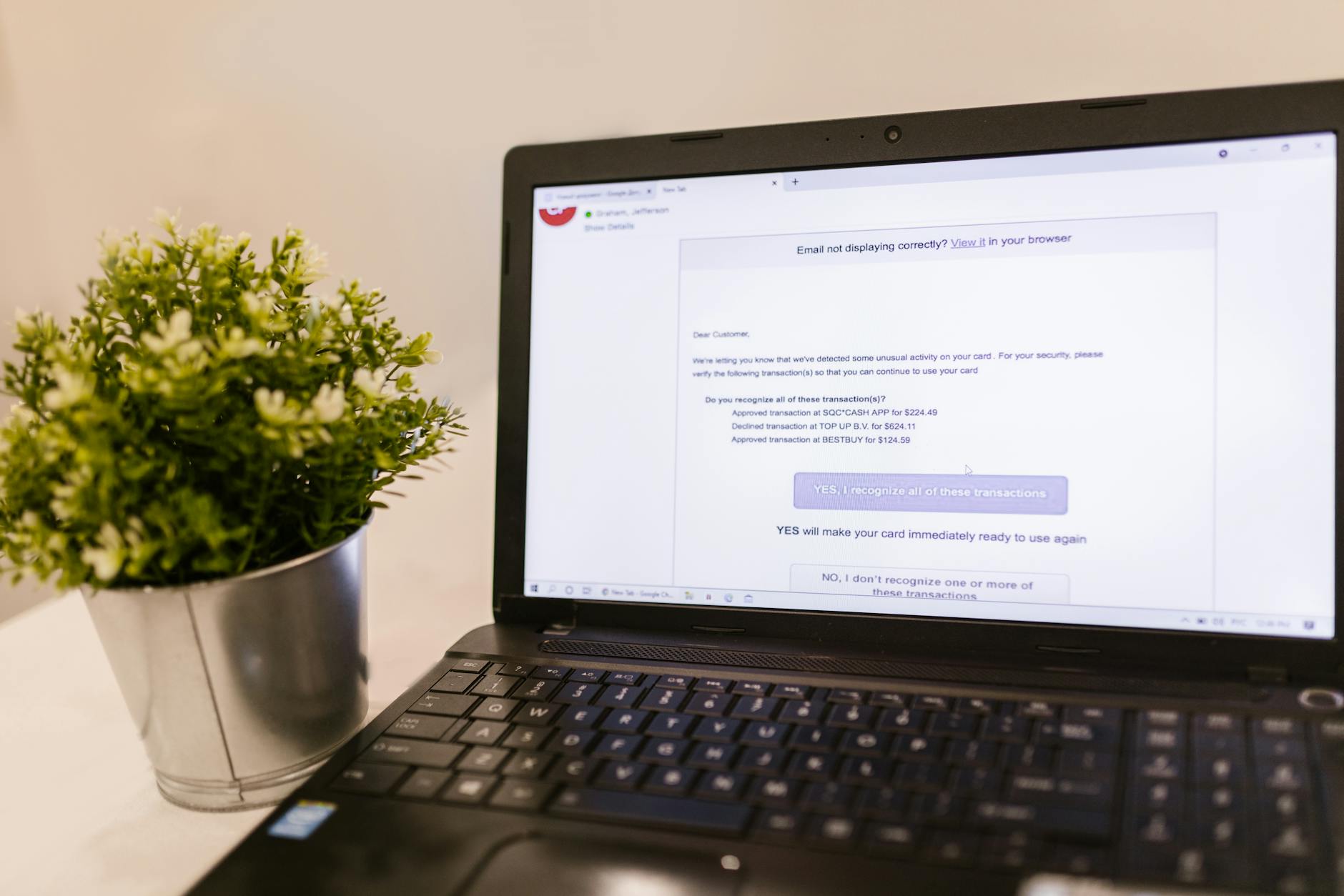
Email Spoofing Detection
Email spoofing — faking the “From:” address to make an email appear to come from a trusted sender — is common in phishing and business email compromise (BEC) cases.
Detection steps:
1. Check the “From:” display address vs. the actual email address (often different in spoofed emails)
2. Examine the “Return-Path:” address — this is where bounces go and often reveals the real sender
3. Check SPF results — did the sending IP match the domain’s authorized senders?
4. Verify DKIM signature — is the cryptographic signature valid for the claimed domain?
5. Trace the “Received:” headers to the originating IP
A spoofed email typically fails SPF and lacks a valid DKIM signature, while originating from an IP address unrelated to the claimed sender’s domain.
Recovering Deleted Emails
Email deletion behavior depends on the client and storage format:
PST/OST files (Outlook): Microsoft Outlook stores email in Personal Storage Table (.pst) or Offline Storage Table (.ost) files. Deleted emails move to the Deleted Items folder. “Permanently” deleted emails move to a hidden dumpster folder or a recoverable items folder (in Exchange environments) before eventual purging. Forensic tools can parse the PST/OST format and recover deleted items from the file’s free pages.
MBOX format (Thunderbird, Apple Mail, many Linux clients): MBOX stores all messages in a single text file. Deleted messages are typically marked with a header flag rather than immediately removed. Forensic parsing of MBOX files can recover deleted message content.
Web-based email (Gmail, Outlook.com): Deleted emails go to Trash and are available for 30 days before permanent deletion. Acquiring webmail evidence requires legal process to the provider or a direct acquisition when the account is logged in on the device.
Exchange Server / Microsoft 365: Email may be retained in litigation hold regardless of what the user does. An organization’s IT admin can often recover deleted email through Exchange admin tools. Legal holds are commonly requested in civil litigation.

Forensic Email Tools
Intella (Vound): Purpose-built for email forensics. Handles PST, MBOX, EML, and MSG formats. Strong search, threading, and timeline visualization.
Nuix: Large-scale data processing and analysis for email-heavy cases (millions of messages).
FTK (AccessData): Broad forensic tool with email parsing capabilities for PST, MBOX, and others.
Aid4Mail: Dedicated email conversion and forensic utility.
FAQ: Email Forensics
Q: Can a forensic examiner tell if an email’s timestamp was changed?
A: Sometimes. The email’s DKIM signature, if present, covers the Date header and other fields. Modifying a DKIM-signed header invalidates the signature. Received timestamps from relay servers are added by third parties and can’t be modified retroactively by the sender.
Q: If I delete an email from my Google account, can Google recover it?
A: Google retains deleted Gmail for some period in its systems even after the trash is emptied. With a valid legal order, Google can sometimes retrieve emails from retention systems. The retention window is not publicly documented.
Q: Can an email’s “Sent” timestamp be faked?
A: The “Date:” header in the email body is set by the sender’s client and can be manipulated. However, the “Received:” timestamps added by mail servers cannot be changed retroactively. An email claiming to be sent at 3 p.m. but received by the first relay server at 7 p.m. has an inconsistency that forensic analysis will catch.
Q: Can cloud providers refuse to comply with subpoenas?
A: Providers may challenge subpoenas on Stored Communications Act grounds, privacy protections, or jurisdictional issues. Federal law enforcement typically uses warrants; civil litigants have more limited access.
Q: Does deleting an email permanently destroy it?
A: Not immediately. Most providers retain deleted items for a defined period. After that window, recovery depends on the provider’s internal backup practices.
Case Example
In a civil dispute, one party alleged digital evidence had been altered after a preservation obligation arose. The forensic examiner compared file system metadata against the litigation timeline and found several files modified after the preservation letter was received. A system cleanup utility had been run during the same period. The examiner documented the specific artifacts indicating post-preservation modifications, distinguishing between routine system operations and deliberate user actions, providing the court with a factual basis for evaluating the spoliation claim.
Practitioner Takeaways
- Cloud data requires separate legal process directed at the provider.
- Document the exact date and time of cloud data acquisition.
- Verify all relevant data types were captured in the provider response.
- Account for timezone differences between cloud logs and device timestamps.
- Preserve authentication logs alongside content data.
See also: Nft Fraud Forensics | Tiktok Forensics | Employment Investigation Forensics
Need Professional Digital Forensics?
Octo Digital Forensics provides expert mobile forensics, data recovery, and digital investigation services for attorneys, insurance companies, and private investigators. Court-admissible reports. Certified examiners.
Contact: octodf.com | info@derickdowns.com | (858) 692-3306