Employee monitoring has expanded dramatically with remote work. Employers want visibility into productivity, security, and compliance. Employees have privacy expectations. Digital forensics sits in the middle — often called in when something goes wrong.
Understanding the legal framework matters for both employers designing monitoring programs and investigators handling employee misconduct cases.
What Employers Can Legally Monitor
Company-owned devices: Employers have broad rights to monitor activity on company-owned computers, phones, and tablets. This includes:
The key precondition: employees must be informed of monitoring through an acceptable use policy acknowledged at hire.
Company networks: Traffic on company-managed networks can be monitored — firewall logs, DNS queries, network flow data, proxy logs. Network monitoring requires no specific employee notification under federal law in most cases.
Company cloud accounts: Microsoft 365, Google Workspace, and Slack provide admin-level audit logs and content access to the company. This is company data, not personal data.

What Employers Cannot Monitor (Generally)
State laws vary enormously. Connecticut, Delaware, and some other states require explicit notification of electronic monitoring. California’s privacy laws create additional obligations. Always consult employment counsel before implementing monitoring.
Employee Monitoring Tools
Endpoint Detection and Response (EDR): Security-focused tools (CrowdStrike, SentinelOne) that monitor file access, process execution, network connections, and potential malicious activity. Primarily security-focused but produce forensic-quality logs.
DLP (Data Loss Prevention): Tools like Forcepoint and Microsoft Purview monitor and can block data transfers — email attachments, USB drives, cloud uploads, and print jobs. DLP logs document exactly what data an employee attempted to move.
Network monitoring: Proxy logs and firewall logs record every external connection from company devices.
Activity monitoring software: Tools like Teramind, Hubstaff, or ActivTrak track active application time, take periodic screenshots, and log keystroke counts (not content, on some configurations). These are common in remote work environments.
Audit logs: Microsoft 365 Unified Audit Log, Google Workspace Admin audit logs, and Slack audit logs record user actions across cloud collaboration platforms — who viewed what, when, and from where.
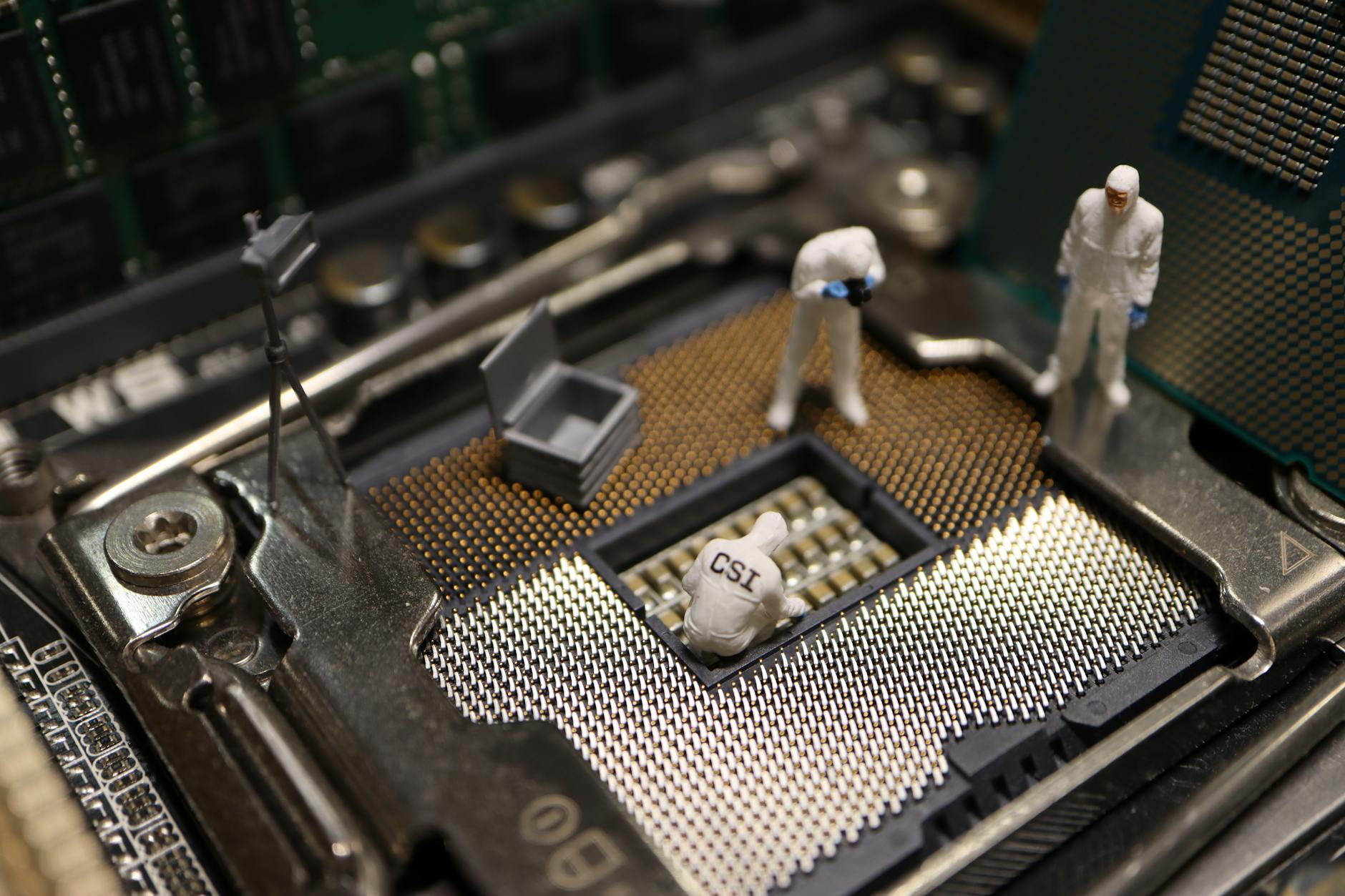
Digital Forensics in Employee Misconduct Investigations
When monitoring tools flag anomalies or a complaint is filed, forensic examination typically follows.
Evidence sources in employee investigations:
Proper Investigation Process
1. Involve counsel early: Attorney-client privilege may protect the investigation from discovery in subsequent litigation
2. Issue litigation hold before imaging: Preserve evidence through proper channels
3. Use forensically sound collection: Hash values, chain of custody
4. Separate investigation from HR action: Don’t let the investigation be seen as a pretext for termination
5. Document every step: If the investigation leads to litigation or law enforcement referral, every step must be defensible
FAQ: Employee Monitoring and Digital Forensics
Q: Can an employee be fired based on forensic evidence from their work computer?
A: Yes, in at-will employment states. The forensic evidence must be collected properly and the investigation conducted fairly. Wrongful termination claims can still arise if the investigation targeted protected activity or was conducted in a discriminatory manner.
Q: What if the employee uses a personal phone for work email?
A: The company email account is company data regardless of the device it’s accessed on. With an MDM profile, the company may be able to wipe only the company data partition. Without an MDM, the company’s options for device-level access are limited.
Q: Do employees have to be told they’re under investigation?
A: Not typically until the investigation is complete. Premature disclosure gives subjects the opportunity to destroy evidence. However, once an investigation concludes and adverse action is taken, employees generally have rights to know the basis.
Q: How long does a typical forensic examination take?
A: Timelines vary based on data volume and case complexity. A single device may take one to three days; multi-device investigations can span weeks.
Q: What certifications should a digital forensics examiner hold?
A: Common certifications include EnCE, CFCE, CCE, and GCFE. Relevance depends on the examination type and the jurisdiction’s expectations.
Case Example
A financial services firm suspected an employee of sharing confidential client data. The forensic examiner imaged the workstation and email archive, revealing unusual file access during the employee’s final two weeks. Email metadata showed communications with a personal account containing attachments matching accessed files. USB device history confirmed a personal storage device was connected during access windows. The evidence was compiled into a report supporting both internal proceedings and civil litigation, leading to a preliminary injunction.
Practitioner Takeaways
- Verify forensic images with cryptographic hashing before analysis.
- Document every examination step for reproducibility.
- Cross-reference findings across multiple artifact types.
- Note tool versions used — behavior changes between versions affect reproducibility.
- Distinguish facts from inferences in your report.
See also: Imessage Database Schema Court Presentation | Testifying Plaintiff Vs Defense | Ip Theft Browser History Case
Need Professional Digital Forensics?
Octo Digital Forensics provides expert mobile forensics, data recovery, and digital investigation services for attorneys, insurance companies, and private investigators. Court-admissible reports. Certified examiners.
Contact: octodf.com | info@derickdowns.com | (858) 692-3306