Android forensics is simultaneously easier and harder than iOS forensics — easier because the platform is more open, harder because Android fragmentation means no single tool works on every device.
With thousands of Android models across dozens of manufacturers, each running different OS versions and security patches, forensic examiners can’t rely on a single method. What works on a Samsung Galaxy S24 won’t necessarily work on a Xiaomi or OnePlus.
Android Extraction Methods
ADB (Android Debug Bridge) extraction: The most common logical method. ADB is a command-line tool built into Android’s developer options. With USB debugging enabled and appropriate permissions, an examiner can pull installed app data, contacts, call logs, and SMS. Most real-world devices don’t have debugging enabled, but enabled-device cases do occur.
Logical extraction via forensic tools: Cellebrite UFED, Magnet AXIOM, and MSAB XRY connect to Android devices and use ADB or proprietary protocols to extract data. Results depend heavily on Android version, manufacturer, and security patch level.
TWRP / custom recovery extraction: On devices where a custom recovery can be booted (typically requiring an unlocked bootloader), examiners can access the full file system directly. Most consumer devices have locked bootloaders.
EDL (Emergency Download Mode) extraction: Qualcomm-based Android devices have a diagnostic mode that can be accessed even when the device is locked. EDL extraction can bypass Android security in some cases, but Qualcomm has progressively restricted access. This method is primarily used by specialized tools.
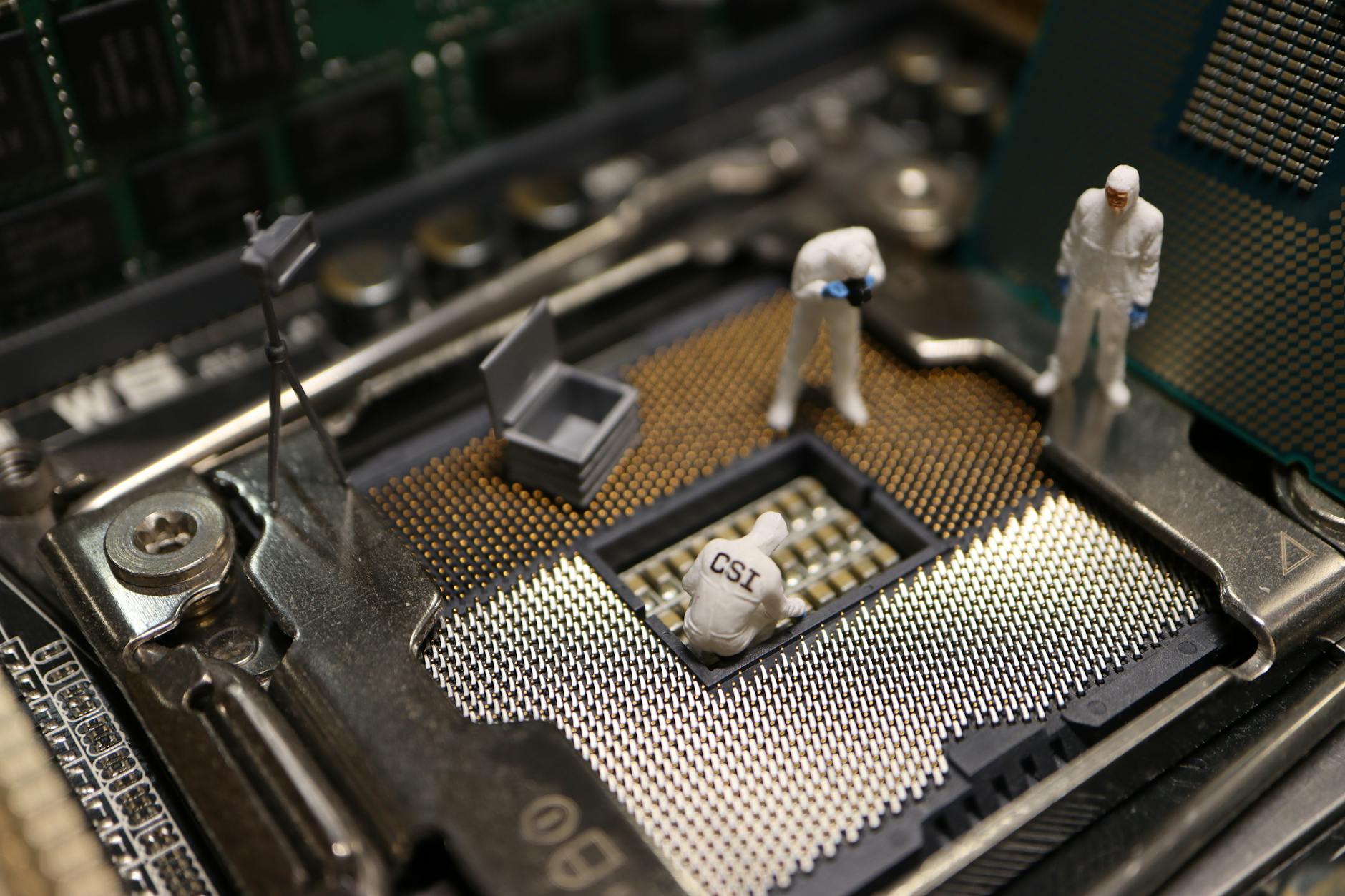
JTAG extraction: A hardware technique that connects test points on the circuit board to read memory directly. Requires technical skill and device-specific knowledge. Produces raw memory dumps that require further processing.
Chip-off: Destructive removal of the NAND chip. Faces the same encryption challenges as iPhone chip-off — data is encrypted with a key derived from the lock screen credential on Android 6.0 and later.

The Fragmentation Challenge
A tool that successfully extracts data from an Android 13 Samsung device may fail completely on an Android 11 OPPO device. This isn’t a failure of the examiner — it reflects the reality of Android’s hardware and software diversity.
Key fragmentation variables:
Android Encryption Since Android 6.0
File-Based Encryption (FBE) became mandatory in Android 9 and later. Each file is encrypted with a key derived in part from the user’s PIN or password. The implication: a locked, fully powered-down Android device is nearly impossible to decrypt without the unlock credential.
Android has two encryption states:
Forensic examiners prioritize seizing Android devices in AFU state — powered on and unlocked — to capture the accessible memory state.
Samsung Knox and Other Security Layers
Samsung devices running Knox add additional security layers beyond standard Android encryption. Knox creates a hardware-backed secure environment that stores sensitive data separately. Some Knox protections survive even a bootloader unlock.
Google Pixel devices running the Titan M2 security chip have similar hardware-backed security that limits what can be extracted even with software-based tools.
FAQ: Android Forensics
Q: Is it true that Android is easier to forensically examine than iPhone?
A: On older devices or unencrypted devices, yes. On modern Android devices with full disk encryption, a strong PIN, and a locked bootloader, they’re comparably difficult. The difference is that older Android devices are far more accessible than older iPhones.
Q: Can factory resetting an Android phone destroy forensic evidence?
A: A factory reset deletes the encryption key, making existing data unrecoverable through software means. However, chip-off with physical analysis might recover some data in specific circumstances. In legal investigations, evidence of a factory reset performed after a crime can itself be significant.
Q: What data can be recovered from a broken-screen Android?
A: If the device is powered on and in AFU state, USB-based extraction can work even without touchscreen functionality. Forensic teams use OTG adapters and special input devices to navigate the screen. If the device is completely unresponsive, JTAG or chip-off are the remaining options.
Q: Does a factory reset make data unrecoverable?
A: On modern devices with hardware encryption, a factory reset destroys the encryption keys, making data practically unrecoverable. On older devices, some data may survive in unallocated storage sectors.
Q: How should a device be handled between seizure and examination?
A: Place it in a Faraday bag, keep it charged, enable airplane mode if accessible, and document its state at seizure. Avoid powering it off if it is already on.
See also: Android Backup Forensics | Nft Fraud Forensics | Tiktok Forensics
Need Professional Digital Forensics?
Octo Digital Forensics provides expert mobile forensics, data recovery, and digital investigation services for attorneys, insurance companies, and private investigators. Court-admissible reports. Certified examiners.
Contact: octodf.com | info@derickdowns.com | (858) 692-3306



