How to Export iPhone Messages as a PDF for Court (The Right Way)
Screenshots of text messages get thrown out of court more often than you’d think.
Not because the messages aren’t real. Because there’s no way to prove they haven’t been edited.
If you’re trying to use iPhone text messages as evidence in a legal case — whether it’s a divorce, a civil dispute, or a criminal matter — the method you use to preserve and present them matters as much as the content itself.
Here’s how to do it right.

Why Screenshots Aren’t Enough
A screenshot is a photo of your screen. Anyone with basic photo editing skills can alter text in a screenshot in under two minutes.
Courts know this. Opposing counsel knows this. A good defense attorney will challenge any screenshot that isn’t backed by a verifiable chain of custody.
What courts want to see is metadata — timestamps embedded in the message file itself, the device identifier it came from, and a hash value that confirms the file hasn’t been touched since it was extracted.
A screenshot has none of that.
Method 1: Use a Certified Forensic Tool (Best for Court)
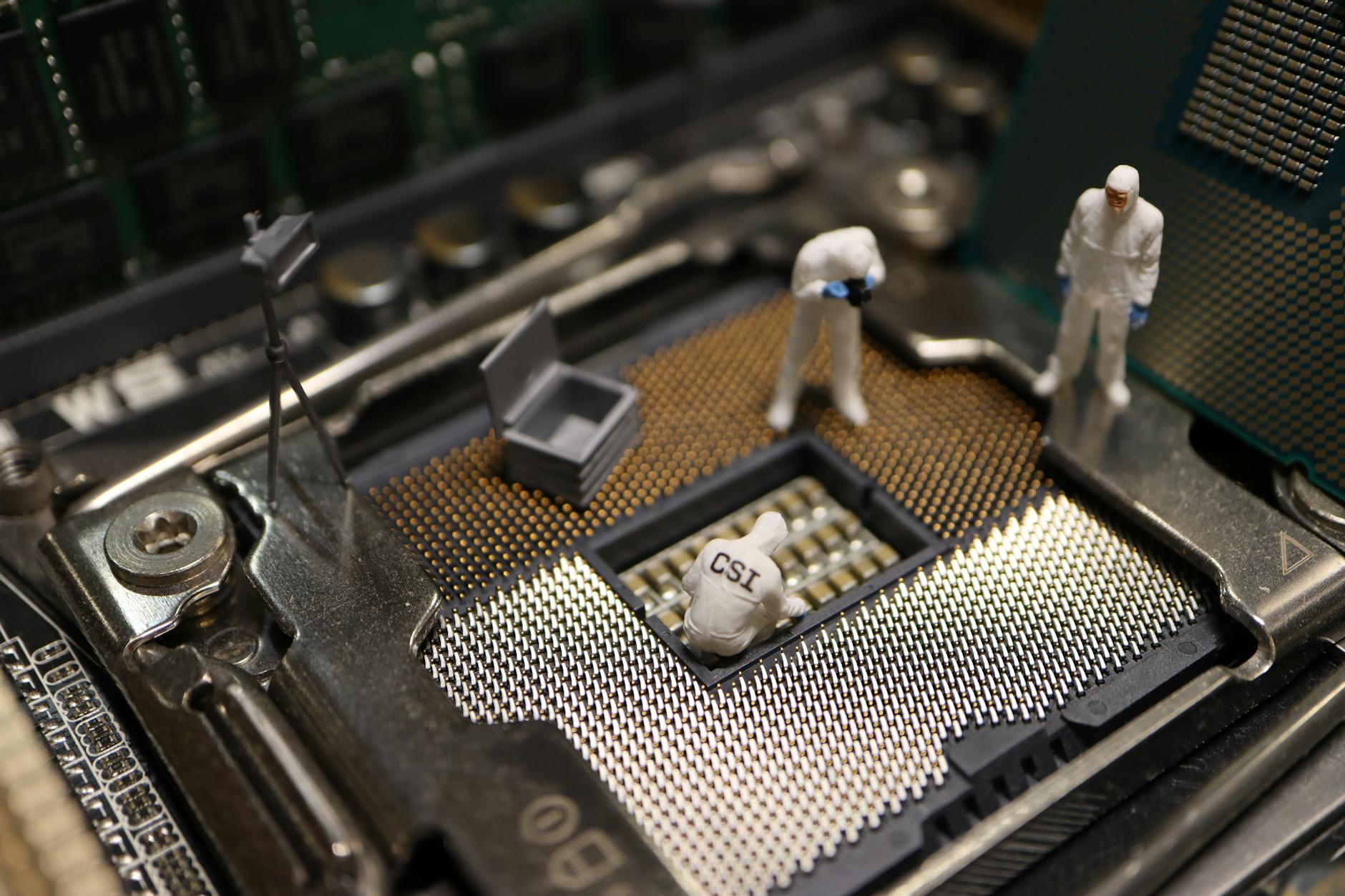
This is the gold standard. Tools like Cellebrite UFED, Magnet AXIOM, and Oxygen Forensic Detective extract messages directly from the iPhone’s file system — not just what’s displayed on screen.
The output includes:
The examiner generates a PDF report from this output that includes their certification, methodology, and a chain of custody log.
This is what courts actually accept without a fight.
Cost: Typically $500-$2,500 depending on scope.
Turnaround: 2-5 business days.
Method 2: Third-Party Apps (Acceptable for Some Cases)
Apps like iMazing, PhoneView, or TouchCopy can export iMessage threads as PDF files with timestamps intact. These are not forensically certified, but they’re better than screenshots.
Use cases where this might work:
What you lose: no hash verification, no deleted message recovery, no expert witness backing.
If there’s any chance the messages will be challenged, go certified.
Method 3: iCloud Backup Export
Apple allows you to request a copy of your iCloud data through privacy.apple.com. This includes iMessages synced to iCloud.
The problem: the export format is a ZIP file of .db and .plist files, not a readable PDF. You’d need software to parse them, and they still won’t have the forensic chain of custody documentation a court expects.
This method is useful for preservation — getting the data off the device before something happens to it — but it’s not a finished court-ready product.
What Courts Look For When Evaluating Text Message Evidence
Judges and attorneys evaluate digital evidence on several factors:
Authentication: Can you prove this message came from this device and this account?
Integrity: Can you prove the content hasn’t been changed since preservation?
Relevance: Does this message actually relate to the matter at hand?
Foundation: Is there someone who can testify about how the evidence was collected?
A forensic examiner satisfies all four. A screenshot satisfies none.
Chain of Custody: Don’t Skip This Step
Even with a certified tool, chain of custody matters.
Document who had the phone, when it was handed to the examiner, when the extraction occurred, and who has had access to the extracted files since. Any gap in that chain can be used to challenge admissibility.
A reputable forensic firm provides a chain of custody log as part of their standard report. If they don’t offer one, find a different firm.
Getting Your Attorney Involved Early
Don’t wait until two weeks before trial to think about this.
The earlier a forensic examiner gets involved, the better. Phones get factory reset. Messages get deleted. iCloud backups get overwritten. Each week that passes is a week of potential evidence loss.
If you think text messages will be relevant to your case, preserve the device now — don’t reset it, don’t update the OS — and get an examiner on the phone.
FAQ
Can I print iMessages directly from my iPhone and use them in court?
You can print them, but they won’t carry much weight without authentication. A printout shows what’s on the screen, not what’s stored in the device’s database. Opposing counsel can and will challenge it.
How long does a forensic iPhone extraction take?
Most standard extractions take 2-5 business days. Complex cases involving locked devices, older iOS versions, or chip-off procedures can take longer. Rush services are often available.
What if the phone is broken or has a cracked screen?
Broken screens don’t prevent extraction in most cases. Forensic tools connect to the device’s hardware directly, not through the screen. Even physically damaged iPhones can often be successfully extracted.
Work With a Certified Examiner in San Diego
Octo Digital Forensics provides certified iPhone extractions with court-ready PDF reports and full chain of custody documentation.
Cellebrite-certified. Serving attorneys, businesses, and individuals throughout San Diego and California.
Visit octodf.com or call 858-692-3306 to discuss your case.
See also: How To Read Cellebrite Report Attorney | Imessage Database Schema Court Presentation | Authenticating Text Messages Fre 901
Need Professional Digital Forensics?
Octo Digital Forensics provides expert mobile forensics, data recovery, and digital investigation services for attorneys, insurance companies, and private investigators. Court-admissible reports. Certified examiners.
Contact: octodf.com | info@derickdowns.com | (858) 692-3306



