meta_title: Quantum Computing and Digital Forensics: What Investigators Need to Know | Digital Forensics Today
meta_description: Quantum computing’s impact on digital forensics: cryptographic vulnerabilities, post-quantum encryption, what quantum computing means for current forensic evidence, and preparing investigations for a quantum future.
slug: quantum-computing-forensics
primary_keyword: quantum computing forensics
secondary_keywords: post-quantum cryptography forensics, quantum threat digital evidence, quantum computing encryption
Quantum Computing and Digital Forensics: What Investigators Need to Know
Quantum computing occupies a unique position in digital forensics: it is both a theoretical threat to current cryptographic foundations and an emerging investigative tool with potential to break encrypted evidence that is currently inaccessible. Understanding where quantum computing is today, what it will realistically be able to do in the near to medium term, and how investigators should be preparing now is essential for anyone who works with long-term digital evidence.
What Makes Quantum Computing Forensically Relevant
The Cryptographic Threat
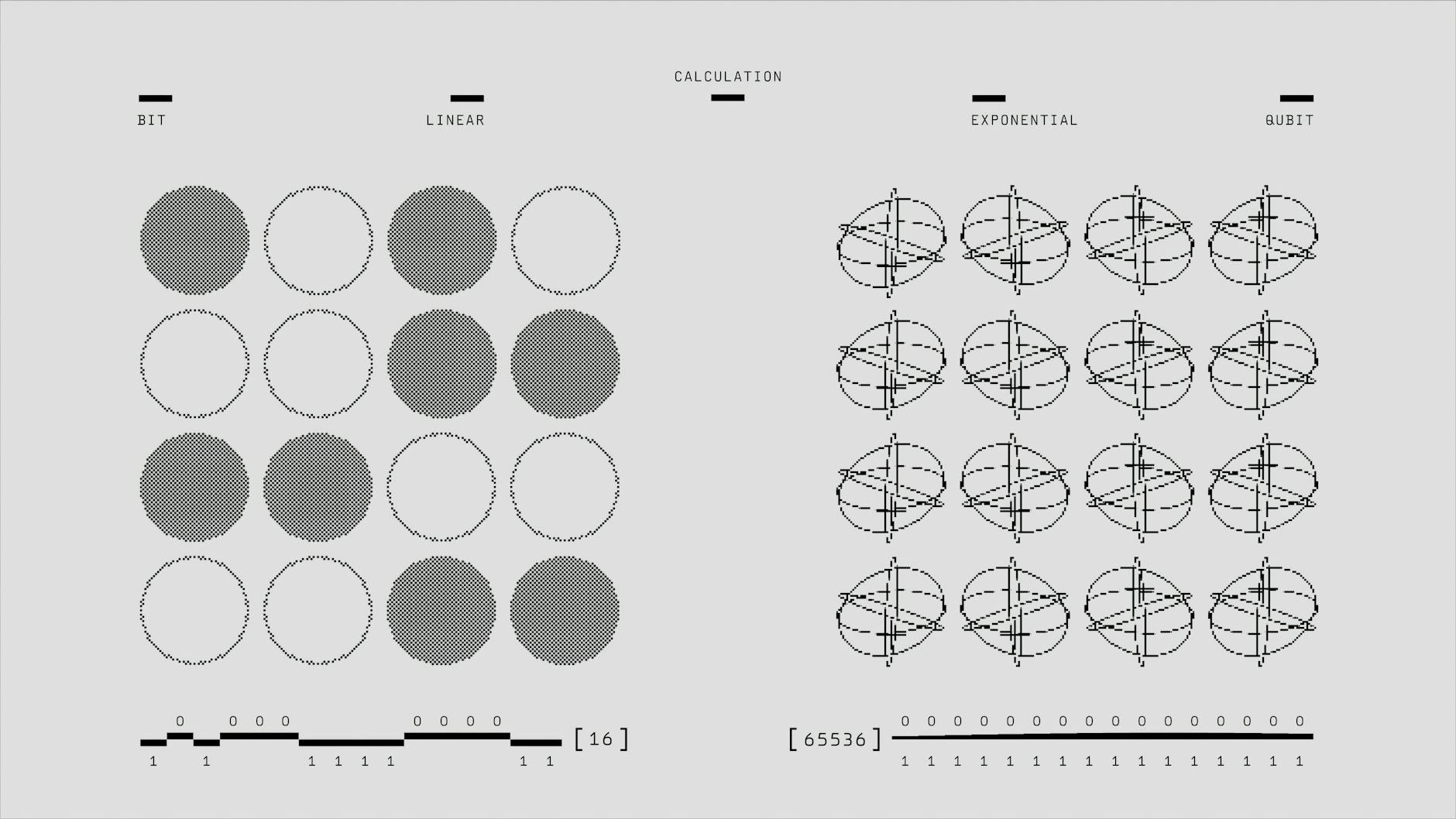
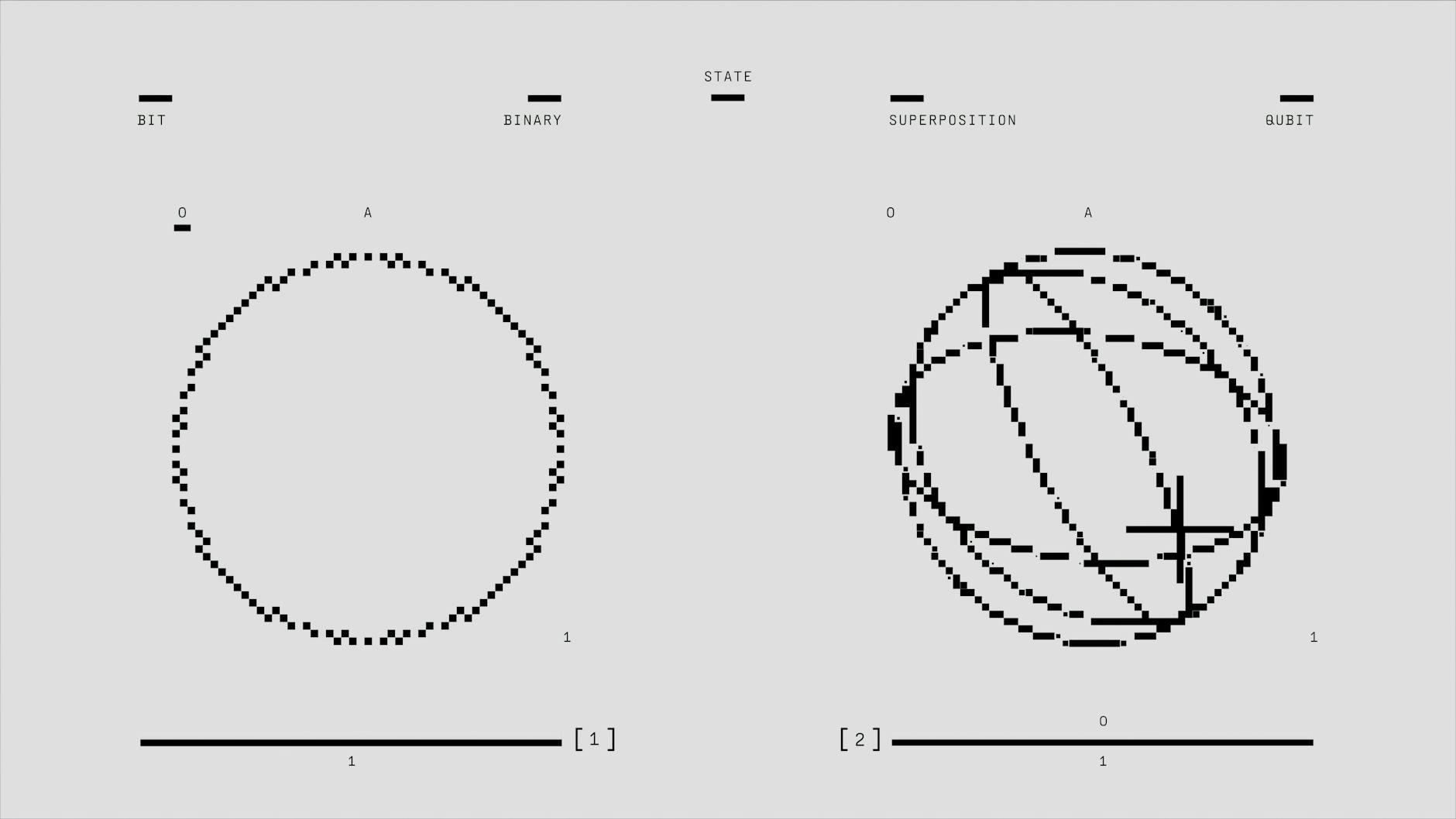
Most modern encryption relies on the computational difficulty of factoring large numbers (RSA) or solving discrete logarithm problems (ECC, the basis of elliptic curve cryptography used in Bitcoin and Signal). Classical computers cannot solve these problems for key sizes currently in use within any practical timeframe.
Quantum computers running Shor’s algorithm can theoretically solve these problems exponentially faster. A sufficiently powerful quantum computer could break RSA-2048 encryption — which currently protects everything from banking to VPNs — in hours rather than the billions of years a classical computer would require.
The Forensic Implication
Evidence that is currently encrypted and inaccessible — a BitLocker drive we cannot decrypt, a Signal database whose key we don’t have, an encrypted Ethereum wallet — may become accessible to quantum decryption in the future. Investigators who preserve encrypted evidence today are creating evidence archives that could become readable as quantum technology matures.
This “harvest now, decrypt later” strategy — collecting and storing encrypted data today with the intent to decrypt it when quantum computers are capable — is reportedly already practiced by nation-state intelligence agencies.
Where Quantum Computing Is Today (2026)
As of 2026, quantum computers are not capable of breaking current encryption standards:
For practical forensic work today: quantum computing is not breaking any currently encrypted evidence. The relevant question is how soon this changes.
Post-Quantum Cryptography and Forensics
NIST’s post-quantum encryption standards are designed to resist both classical and quantum attacks. As these standards are adopted:
For investigators: Evidence encrypted with post-quantum algorithms will be significantly more durable against future quantum attacks. Devices and systems adopting PQC now are preparing for a future where quantum computers can break current standards.
For long-term evidence storage: Forensic evidence archives — particularly encrypted evidence expected to be held for decades — should be re-encrypted with post-quantum algorithms as they become available in forensic tools.
For blockchain: Bitcoin and Ethereum currently use elliptic curve cryptography (ECDSA) which is vulnerable to Shor’s algorithm. The cryptocurrency community is actively developing quantum-resistant signature schemes. Evidence collected from blockchain transactions today — the transaction records themselves on the public ledger — are not encrypted and will remain readable. The private keys that control wallets are the vulnerability.
Quantum Computing as an Investigative Tool
Beyond the threat to existing encryption, quantum computing may eventually enable:
Accelerated password cracking: Quantum computers running Grover’s algorithm can search an unstructured database quadratically faster than classical computers. This could reduce the time to brute-force passwords, though the advantage is less dramatic than Shor’s algorithm for factoring.
Optimization problems: Routing complex financial transaction traces, optimizing blockchain graph analysis, and accelerating pattern matching in large datasets are areas where quantum advantage may help investigators before full cryptographic capability is reached.
Simulation: Quantum simulation of molecular and physical systems could improve the modeling of timing attacks and side-channel analysis used in some forensic decryption approaches.
Preparing Forensic Practice for the Quantum Era
Evidence preservation strategy
Investigators handling cases with long-term significance should preserve encrypted evidence even when it cannot currently be decrypted. Document the encryption type and key size to enable future decryption attempts as technology advances.
Chain of custody longevity
Evidence expected to be relevant for decades needs chain of custody documentation that will remain legible and verifiable long after the original examiners have retired. Digital signature schemes used to authenticate forensic evidence chains should use post-quantum resistant algorithms.
Client counseling
Attorneys and clients who have encrypted evidence or need to protect communications against future quantum decryption should be counseled to adopt post-quantum encryption standards now for their most sensitive data.
FAQ
Should I be worried about a quantum computer breaking my BitLocker drive today?
No. Current quantum computers cannot break BitLocker’s AES-256 encryption, which is considered quantum-resistant because Grover’s algorithm only halves the effective key size (making AES-256 equivalent to AES-128 against a quantum attacker). RSA and ECC keys are the vulnerable ones, and current quantum computers cannot break those either.
Is any current encryption quantum-safe?
AES-256 symmetric encryption provides reasonable quantum resistance. SHA-256 and SHA-3 hash functions are considered quantum-resistant. The vulnerable algorithms are asymmetric (RSA, ECC, Diffie-Hellman). NIST’s post-quantum standards provide new asymmetric algorithms that are quantum-resistant.
How does quantum computing affect Bitcoin specifically?
Bitcoin addresses derived from elliptic curve public keys are vulnerable to quantum attack via Shor’s algorithm once a sufficiently powerful quantum computer exists. The Bitcoin community has not yet deployed a quantum-resistant signature upgrade. Funds in exposed Bitcoin addresses (where the public key is revealed) are potentially at risk from a quantum attacker; funds in addresses where only the hash of the public key is public have an additional layer of protection until a transaction is made.
Future-proofing your digital evidence strategy for a post-quantum environment?
Octo Digital Forensics stays current on emerging cryptographic threats and evidence preservation best practices. Consult with our team on long-term evidence archiving strategy.
Visit [octodigitalforensics.com](https://octodigitalforensics.com).
See also: Nft Fraud Forensics | Tiktok Forensics | Employment Investigation Forensics
Need Professional Digital Forensics?
Octo Digital Forensics provides expert mobile forensics, data recovery, and digital investigation services for attorneys, insurance companies, and private investigators. Court-admissible reports. Certified examiners.
Contact: octodf.com | info@derickdowns.com | (858) 692-3306



